192.168.1.100: The Secret Network Gateway Accessing Port 8080 Behind the Corporate Firewall
192.168.1.100: The Secret Network Gateway Accessing Port 8080 Behind the Corporate Firewall
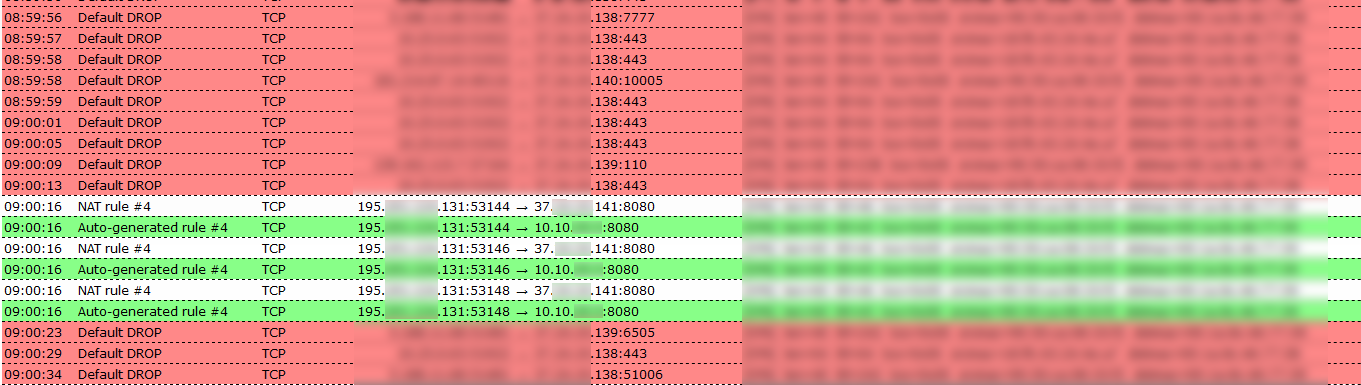
Every small network whispers quiet authority—open ports, hidden access points, and the unseen traffic that keeps operations flowing. Among the most commonly referenced IP addresses in business and home network setups is 192.168.1.100, often acting as a key pivot in localized communication, particularly when communication paths converge at port 8080. This article reveals how 192.168.1.100 serves not just as a device identifier, but as a gateway proxy to secure, application-level traffic routed through port 8080—an endpoint frequently used in modern web services, internal APIs, and cloud-connected tools.
Understanding its role unlocks insight into both network architecture and digital workflow efficiency.
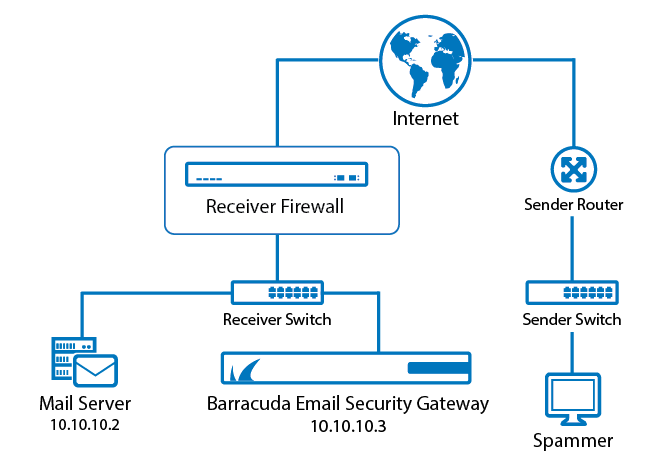
At first glance, the IP address 192.168.1.100 appears standard—part of the widely recognized 192.168.1.0/24 private IP range, reserved for local area networks. But within enterprise environments, this address often functions as a dedicated gateway host or reverse proxy.
Deploying services through port 8080—typically the de facto standard for HTTP-based web interfaces on non-standard ports—this device bridges internal network resources and external access. Such configurations are common in IT infrastructure, where security and traffic control are paramount. As one network engineer noted, “Routing traffic from 192.168.1.100 through port 8080 allows organizations to expose internal tools to approved users without opening public-facing ports, reducing attack surface.”
How Port 8080 Powers Modern Internal Services
Port 8080 is far more than a footnote in server configuration—it is a linchpin for accessible, secure web of internal applications.Used predominantly as an alternative to port 80, it enables HTTP traffic on non-standard channels, avoiding common firewall conflicts and simplifying in-house routing logic. Services listening on this port commonly support web dashboards, API endpoints, and cloud integration portals.
Examples include internal content management systems, real-time collaboration tools, and internal API gateways.
These applications leverage port 8080 to avoid interruptions from publicly blocked ports, allowing internal users to interact seamlessly via familiar browser URLs—typing http://192.168.1.100:8080 instead of hard-to-remember or restricted addresses. According to network architecture guidelines, this setup enables dynamic access control: only authenticated internal devices (identified via VLAN tags, MAC filtering, or session tokens) reach the service, enhancing security without sacrificing usability.
- Security Through Obfuscation: By masking critical services behind the default 80/443 ports and using 8080 as an intermediary, organizations reduce automated scanners’ ability to detect entry points.
- Scalability: Port-based routing allows load balancing across multiple instances of the same service hosted behind 192.168.1.100, ensuring high availability.
- Simplified Management: When errors or updates occur, administrators deploy fixes directly to the gateway, rather than dozens of endpoint devices.
The choice of 192.168.1.100 as a central proxying node reflects a broader trend: consolidating network access through logical gateways rather than brute-force exposure. This model supports zero-trust principles, where trust isn't given but verified through layered authentication and device posture checks.
Security professionals argue that deploying a managed proxy on this IP—intercepting traffic via port 8080—creates a critical checkpoint that balances openness with control.
Real-World Use Cases: Bringing Remote Teams into the Loop
In today’s distributed work environments, 192.168.1.100:8080 serves as a virtual visa into internal digital ecosystems. Remote employees connecting from offsite locations often access this endpoint via secure internal VPNs or direct LAN connections, allowing them to interact with internal dashboards, file repositories, and monitoring tools as if physically present.For example, a distributed IT team might deploy a real-time monitoring portal responsive on port 8080.
Through 192.168.1.100:8080, engineers in Seattle or Berlin view live system statuses, receive alerts, and deploy patches without needing direct server logins or exposing backend infrastructure. Such models minimize credential sharing risks and streamline support workflows. One digital transformation lead described it: “Using 192.168.1.100 and port 8080 lets our global team operate cohesively—security kept tight, yet access fluid.”
The design also facilitates automation: CI/CD pipelines, internal service discovery tools, and monitoring agents adjust dynamically to changes behind the proxy, reducing manual configuration overhead.
As network complexity grows, central gateways like 192.168.1.100 become essential scaffolding—keeping systems scalable, resilient, and secure.
Best Practices for Securing 192.168.1.100:8080 Communication
Protecting access to 192.168.1.100:8080 demands a layered security approach. Simply exposing a port behind a local IP is insufficient without rigorous controls.Organizations implement several recommended practices to safeguard this gateway:
- Network Segmentation: Isolating the deployment environment using VLANs or firewalls limits exposure to trusted subnets and internal users only.
- Authentication & Authorization: Integrating the gateway with RADIUS or LDAP validates each user and device identity before granting access.
- Rate Limiting & Rate Limiting: Preventing abuse involves capping request rates, especially critical for services handling sensitive operations.
- Encrypted Traffic: Enforcing TLS termination at the gateway ensures data remains protected in transit, even within the private network.
- Regular Auditing: Monitoring access logs detects anomalies and supports incident response, reinforcing accountability.
These measures collectively transform 192.168.1.100:8080 from a passive port into a managed, audited access point—essential for enterprise-grade network hygiene. “Every layer of protection strengthens trust,” states a chief information security officer. “Hosting critical services behind a secure, monitored gateway is no longer optional—it’s foundational.”
/*In an age of cloud abstraction and remote connectivity, understanding how IPs like 192.168.1.100 and ports like 8080 function reveals the quiet backbone of digital operations.
These configurations bridge usability with security, accessibility with control—ensuring networks remain both robust and user-focused. The future of enterprise networking lies not just in innovation, but in the precision of such hidden gateways.
*/


Related Post

Sheri Moon Zombie: From Cult Icon to Torchbearer of Art and Advocacy — A Life Forged in Fire

Is Emily Compagno Engaged? The Truth Behind the Waiting Game

<strong>Unveiling Brandi Passante Hot Pics: The Iconic Image Campaign That Redefined Beauty & Boldness</strong>
Does August Brooks Have Cancer? Unveiling the Silent Fight Behind the Headlines