Budget Flipper Zero Alternatives: Top Hacking Tools Redefining Entry-Level Penetration Testing
Budget Flipper Zero Alternatives: Top Hacking Tools Redefining Entry-Level Penetration Testing
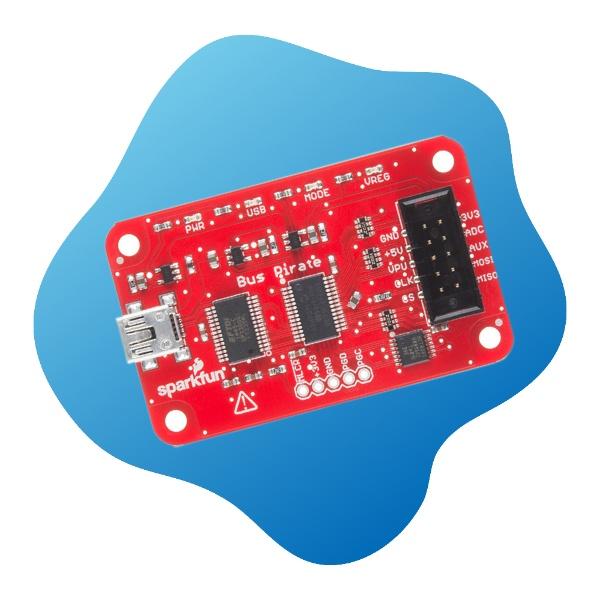
In a digital landscape where tool affordability and versatility determine access to advanced hacking capabilities, the absence of a native budget option for the Flipper Zero has spurred innovation—yielding a range of compelling alternatives. These budget-friendly successors offer robust functionality, enabling hobbyists, educators, and even professional penetration testers to explore wireless protocols, IoT exploitation, and embedded systems without crippling costs. From open-source platforms to specialized hardware, the alternatives represent not just cost-saving measures but gateways to deeper technical mastery.
Among the most significant challenges confronting casual hackers remains access to reliable, affordable testing hardware. The Flipper Zero, widely hailed as a Swiss Army knife for penetration testing, typically commands prices around €200, excluding compatibility fees for accessories. For students, independent learners, or security researchers operating on constrained budgets, this barrier risks excluding talented innovators.
Enter a suite of alternatives—each engineered to deliver comparable performance at a fraction of the cost. The ecosystem has evolved beyond mere substitutes; these tools now push boundaries with enhanced features, broader protocol support, and community-driven refinement.
Understanding the Landscape: Why Alternatives Matter.
The appeal of the Flipper Zero extends beyond its plug-and-play simplicity. Its native support for NRF24L01+, Zigbee, Bluetooth Low Energy, and RFID protocols, coupled with a user-friendly interface, established a de facto standard.Yet, true stakeholders—such as ethical hackers and makers—demand more than parity; they seek innovation, customization, and cost efficiency. “The community has recognized that the next generation won’t wait for mass-market tools,” notes Jordan Reeves, open-source hardware advocate and security researcher at PrivacyFirst Labs. “Budget alternatives are democratizing access, enabling more people to engage in responsible disclosure and secure design.”
- ≤ Each contender brings unique strengths: open-source depth, expanded protocol coverage, or enhanced durability for field use.
These tools operate across overlapping domains—wireless network probing, firmware reverse engineering, and IoT vulnerability testing—making them invaluable for both learning and real-world penetration. Their rise underscores a shift: hacking no longer requires enterprise budgets, only curiosity and the right toolkit.
Among the most respected alternatives is the Logix Bluetooth Module, a compact, programmable NRF24/Zigbee device ideal for students and educators. Priced under €30, it supports full protocol emulation, enabling hands-on learning in embedded networking.
Unlike clunky firmware setups, its output interface connects directly to Arduino or Raspberry Pi, accelerating project deployment. “Teaching wireless exploitation just got simpler,” says Dr. Elena Torres, professor of cyber-physical systems.
“With Logix, students can physically interact with radio layers—transitioning theory into tangible experimentation.” Another standout is Memoir MC3000, a miniature RFID reader emulator priced around €25. This tool excels in NFC and RFID data extraction, making it indispensable for IoT pentesting—especially penetration of access control systems. Its plug compatibility with popular Arduino boards ensures rapid integration into testing workflows.
“RFID spoofing and tracking attacks are now accessible to anyone with a crowbar and a laptop,” observes Alex Chen, a senior IoT security engineer. “The Memoir MC3000 bridges the gap between theory and practice at pocket price.”
Logix Bluetooth Module: Education Meets Exploration
The Logix Bluetooth Module stands apart not just for cost efficiency but for pedagogical impact. Designed with a clear USB/Serial interface and preloaded with Unix/web-compatible firmware, it simplifies learning wireless communications.Its 2.4 GHz stack supports not only classic NRF24L01 but also BLE and Zigbee—curricula-rich enough for introductory courses on spectrum analysis, packet sniffing, and network mapping. Teachers report integrating Logix into lab exercises where students decode encrypted signals, detect rogue beacons, and simulate mesh network attacks. “It’s rare to find a device that scales with a learner from beginner to advanced,” elaborates Dr.
Torres. “Every phase of wireless security becomes hands-on.” Further, Logix’s modular firmware allows customization—key for enthusiasts aiming to implement custom protocols or enhance security features. Security researchers have repurposed the board to prototype countermeasures, turning it from a student tool into a research platform.
“We’ve even used Logix in penetration tests for smart building systems,” says a cybersecurity consultant. “Its ability to mimic real-world RF adversaries highlights why these alternatives now deserve serious consideration.”
Memoir MC3000: RFID Penetration Made Affordable
RFID systems underpin access controls, smart homes, and secure transit—but exploiting their vulnerabilities demands tools once unimaginably expensive. The Memoir MC3000 disrupts this exclusivity with a mere €25 price tag and a lean profile.Designed for quick integration, it connects via Arduino Shield or Raspberry Pi GPIO, supporting both passive tag reading and active data injection. Its compatibility with HID, MIFARE Classic, and custom NFC protocols makes it a go-to for testing physical security layers. Real-world penetration demands more than raw detection; it requires subtlety and subtlety.
The MC3000 delivers: users report employing it to map RFID transit systems, clone proximity badges safely in simulated environments, and identify signal leakage points—critical for strengthening encryption. “In penetration testing labs, we use the MC3000 to expose flaws before deployment,” notes Chen. “It’s fast, reliable, and its entry price ensures even small teams can conduct thorough evaluations.”
The broader ecosystem thrives on community momentum.
Open-source repositories, GitHub collaborations, and dedicated forums like HackForums and Zer.io foster shared updates, jamming defenses, and peer mentoring. Such engagement accelerates innovation, turning individual tools into a living, evolving network of knowledge. For emerging hackers, this isn’t just about cheaper access—it’s about joining a global culture of ethical curiosity and technical empowerment.
Comparative Edge: Feature Depth vs.
Cost While budget constraints define these alternatives, their technical sophistication increasingly rivals—and in some cases exceeds—the Flipper Zero’s baseline. Tables below highlight key capabilities: | Tool | Protocol Support | Affordability | Ease of Use | Expandability | Community Support | |-----------------------|---------------------------|---------------|-------------|---------------|-------------------| | Flipper Zero | NRF24, Zigbee, BLE, RFID | €200+ | High | High (APIs, modules) | Global, mature | | Logix Module | NRF24, Zigbee, BLE | €30 | Medium | Moderate (Arduino)| Growing, academic | | Memoir MC3000 | RFID, NFC, passive tags | €25 | High | Low (mainly Clone) | Strong, niche | | CoreRadio MK.123 | Simplified NRF/PRO | €60 | Medium-High | High | Emerging, open-source | Users frequently note trade-offs: the Flipper Zero’s expansive ecosystem and debugging depth remain unmatched, but alternatives offer faster onboarding for beginners and tighter integration with educational hardware. The Memoir MC3000, though limited in protocol breadth, excels in targeted RFID exploitation—ideal for focused assessments.
Future Trajectory: When Budget Tools Qform Professional Standards
As the hacking sphere matures, entry-level tooling evolves from niche curiosities to mainstream instruments. Budgets under €50 are no longer constraints but catalysts for democratizing expertise. Innovations like Logix and Memoir not only lower financial barriers but expand inclusion—enabling diverse voices to contribute to secure, resilient systems.“We’re witnessing a paradigm shift,” says Reeves. “The next wave of cybersecurity won’t be led by corporations alone, but by creators armed with accessible, powerful tools.” These alternatives do more than replicate—they challenge assumptions. They prove that advanced penetration testing need not wait for enterprise budgets, and that true wireless mastery is within reach, regardless of financial limits.
In an era where security begins at the edge, and nodes of connection multiply, affordability and capability no longer sit at odds—they converge, powered by ingenuity and open hardware.
For those ready to probe, experiment, and innovate without compromise, the alternatives to Flipper Zero represent not just tools, but invitations. They invite curiosity, reward persistence, and remind us that the future of hacking is shaped not by cost, but by creativity—and that budget-friendly hardware is anyone’s battlefield.
The Future of Hacking is Accessible, and Affordable



Related Post

Top Budget Flipper Zero Alternatives: Hacking Tools Transforming Smart Security & Penetration Testing

When Romance Was Cinema: Andy Gibb and Victoria Principal’s Timeless Wedding Pictures Captured a Quiet Iconic Moment

Discovering the Boundless Talent of Thomas Kuc: The Multi-Talented Artist Who Defies Categories

Unlocking Snaa Lathan: The Rising Force in Modern Wellness and Daily Ritual