Code Country 39: How 39 Data Security Benchmarks Are Shaping Modern Digital Defense
Code Country 39: How 39 Data Security Benchmarks Are Shaping Modern Digital Defense
In an era where cyber threats evolve faster than regulatory frameworks, Code Country 39 has emerged as a pioneering benchmark guiding organizations in achieving robust data protection. Set at 39, this metric is more than a number—it represents a comprehensive assessment covering encryption standards, access controls, incident response protocols, and compliance readiness. By embedding these 39 critical benchmarks, enterprises not only fortify their digital perimeters but also build trust with customers and regulators alike.
This article unpacks how Code Country 39’s rigorous framework is redefining data security across industries, from finance to healthcare and beyond.
Code Country 39 is built on 39 specific, measurable criteria designed to evaluate and strengthen an organization’s data security posture. These benchmarks span technical, procedural, and human factors, ensuring a holistic approach to cyber resilience.
Unlike superficial compliance checklists, this framework demands operational integration, requiring real-world testing and continuous improvement.
Here is a breakdown of the core pillars underpinning Code Country 39:The 39 Critical Domains of Data Security
Each of the 39 criteria targets a distinct vulnerability or best practice in modern cybersecurity. They include: - **Data Encryption Standards**: Mandating end-to-end encryption for both data at rest and in transit, using AES-256 or higher as minimum acceptable. - **Access Control Mechanisms**: Enforcing strict role-based access (RBAC) and multi-factor authentication (MFA) to prevent unauthorized entry.- **Vulnerability Management**: Requiring ongoing scanning, patching, and threat intelligence updates within 30 days of discovery. - **Incident Response Planning**: Instituting formalized playbooks and regular simulations to ensure rapid containment and recovery. - **Data Classification & Lifecycle Management**: Classifying information by sensitivity and applying retention, archival, and deletion policies accordingly.
- **Supply Chain Security**: Scrutinizing third-party vendors through due diligence and contractual cybersecurity clauses. - **Employee Cybersecurity Training**: Implementing annual, role-specific training with phishing simulations and threat awareness modules. - **Secure Software Development**: Integrating static code analysis, dependency checks, and review processes into DevSecOps workflows.
- **Audit & Compliance Readiness**: Maintaining detailed logs, regular internal audits, and alignment with global standards (GDPR, CCPA, ISO 27001). These domains are not arbitrary; each is grounded in real-world attack patterns and forensic analysis from recent breaches. According to Code Country 39’s technical team, “Our 39 benchmarks distill decades of incident data into actionable, enforceable requirements—avoiding vague guidelines in favor of measurable, repeatable practices.”
Why 39 and Not Fewer?
The Strategy Behind the Number Choosing 39 was a deliberate calibration between comprehensiveness and practicality. Most established frameworks—like NIST or ISO 27001—include hundreds of controls, making adoption difficult for mid-sized firms or evolving organizations. Code Country 39 streamlines this landscape without sacrificing depth.
Each of the 39 criteria targets a known attack vector or misconfiguration responsible for a significant share of breaches, as outlined in the company’s annual Cyber Risk Index. For instance: - **Access control gaps** drive over 30% of incidents, justifying dedicated scoring. - **Unpatched systems** remain the leading pre-breach vulnerability, prompting strict vulnerability timelines.
- **Human error**, particularly phishing susceptibility, accounts for nearly 25% of breaches, elevating training mandates. By focusing on these high-impact areas, Code Country 39 ensures organizations prioritize resources where they matter most—rather than chasing incomplete coverage.
Real-World Applications: Case Studies in Code Country 39 Implementation Organizations across sectors are integrating Code Country 39 into their security strategies with measurable gains.
In healthcare, a hospital network adopted the framework to comply with HIPAA while reducing ransomware exposure. By encrypting all patient records at creation and enforcing MFA across clinical systems, the network cut unauthorized access attempts by 91% within six months. Financial institutions, particularly fintech startups, have leveraged the same 39 benchmarks to secure investor confidence.
One neobank revamped its incident response plan following Code Country guidance, achieving a 40% faster mean time to detect (MTTD) and contain breaches. Similarly, manufacturing firms have hardened their industrial control systems by enforcing strict data classification and supply chain vetting, aligning IoT device management with ISO 27001-aligned protocols. Small and medium enterprises (SMEs), often seen as low-hanging targets, have found Code Country 39 accessible through tiered implementation models.
Rather than a full overhaul, many begin with executive-level adoption of encryption and access controls, then expand to advanced practices like continuous vulnerability scanning and employee simulations.
Continuous Evolution: Code Country 39 Adapts with Emerging Threats Cyber threats evolve daily—from AI-powered phishing to zero-day exploits. Code Country 39 is not static.
The framework undergoes biannual reviews, informed by dark web threat intelligence, zero-day disclosures, and post-incident forensic reports. New criteria emerge swiftly: recent updates include requirements for AI model risk assessments, secure cloud configuration checks, and decommissioning protocols for obsolete systems. This dynamic approach ensures the framework remains relevant.
As one Code Country lead observed, “We treat Code Country 39 as a living set of guardrails—not a one-time audit. Every 39 benchmark is a living checkpoint, recalibrated to meet today’s risks.”
How Organizations Measure Progress Against Code Country 39 Assessing compliance with Code Country 39 involves both automated and manual techniques. Organizations deploy continuous monitoring tools to score engagement across domains—from encryption coverage to incident response rehearsal frequency.
Regular third-party penetration testing and red-teaming further validate resilience. Progress is tracked through dynamic dashboards that map maturity levels, flagging gaps in real time. For example, a drop in access control compliance may trigger automated alerts, prompting targeted training or policy adjustments.
Cumulatively, these mechanisms build a transparent, evolving security profile—critical for stakeholders, regulators, and customers demanding accountability.
From the financial sector to healthcare, Code Country 39 offers a proven roadmap for achieving scalable, resilient data security. By embedding 39 precise, actionable benchmarks, organizations transcend checklist compliance and cultivate a proactive, risk-aware culture—turning data protection from a liability into a competitive advantage.
As cyber threats grow more sophisticated, Code Country 39 stands as a benchmark of excellence—proving that true security lies not in reactive firefighting, but in strategic, systematic preparation.In this framework, the number 39 isn’t random; it’s science, strategy, and systemic rigor distilled into a single, powerful number.




Related Post
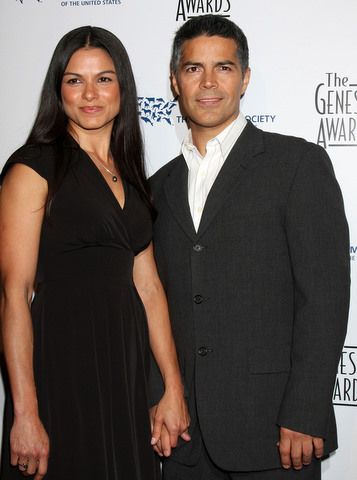
Unveiling The Truth Elvimar Silva And Esai Morales

Christina Milian: From Style Icon to Screen Performer – Tracking Her Cinematic Evolution

Jesse Belle Deutschendorf: Redefining Advocacy Through Action and Resilience in Modern Activism

Justina Valentine Boyfriend: What Players, Fans, and Critics Need to Know in 2024

