Fix 403 Forbidden in Docker: Master Nginx Reverse Proxy Secrets on Containers
Fix 403 Forbidden in Docker: Master Nginx Reverse Proxy Secrets on Containers
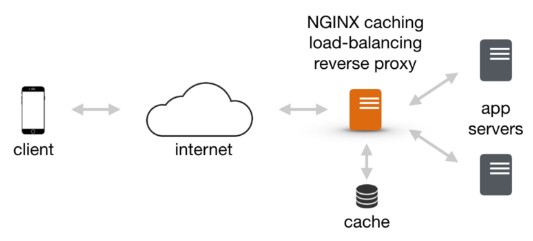
When a web app fails with a 403 Forbidden error inside a Dockerized Nginx environment, developers confront a common but opaque roadblock that halts access and frustrates users. This HTTP status signals that while the server understands the request, it refuses to authorize it—often due to configuration oversights in reverse proxy setups between containers. Nginx, the standard proxy in most Docker deployments, plays a pivotal role here; misconfigured rules, missing access directives, or clashing network policies within containerized services can trigger 403 responses unexpectedly.
Understanding the root causes and applying precise fixes transforms these errors from hidden bugs into manageable system states.
At the core of 403 errors in Docker-Nginx stacks are permission mismatches and proxy misstraps—orchestrated by container isolation and network segmentation. Nginx inside Docker runs as a lightweight process with a constrained filesystem and distinct network namespace.
When proxy configurations are incomplete or fail to align with container routing logic, Requests are denied access despite valid backend endpoints. Common pain points include improper type fixtures, missing headers (such as `X-Forwarded-For`), and mismatched SSL settings.
Core Causes of 403 Forbidden in Dockerized Nginx
Not all 403 errors stem from access control lists alone—context in Docker adds layers. Key contributors include: - **Missing `X-Forwarded-For` headers**: Without these, Nginx loses the client’s original IP, risking authorization failure.- **Incorrect access control directives**: Mismatched location blocks or missing `allow/hide` rules block valid requests. - **Ineffective reverse proxy chain**: Nginx ensemble or upstream misconfiguration blocks downstream service access. - **Port exposure timing**: Traffic hits a container before it’s ready, especially in dynamic orchestration like Docker Compose or Kubernetes.
- **Resource binding conflicts**: Containers bound to private or `127.0.0.1` addresses block external proxy firewalls.
The interdependency of these factors explains why 403 errors feel elusive—fixing one element (e.g., adding headers) may not resolve the symptom without adjusting upstream logic. This complexity demands a methodical diagnostic approach.
Step-by-Step Fix: Removing the 403 Barrier
Diagnose the Root Cause Before modifying configs, gather actionable data.Use Docker’s `--log-driver` and `docker logs
Tools like `tcpdump` or `t cleaning`’s `status | grep access` help identify rejections early. Tweak Proxy Headers with Confidence Nginx’s `proxy_set_header` directives are your first defense. For secure proxy forwarding, include: ```nginx proxy_set_header Host $host; proxy_set_header X-Real-IP $remote_addr; proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for; proxy_set_header X-Forwarded-Proto $scheme; ``` Crucially, trigger `X-Forwarded-For` by setting `proxy_http_version 1.1;` and ensuring upstream servers truthfully read the header.
Without `X-Forwarded-For`, Nginx may block requests as “untrusted,” even from internal services. Legal operations rely on correctly pass255_ip if behind NAT—never disable `allowed_ip` without assessing exposure risks. Refine Location and Routing Expressions Invalid `location` blocks starve routes of rules.
Ensure your `nginx.conf` mirrors actual container IPs and proxy setups. Use `order`, `if` conditions, and `hide` directives wisely. For example, a multi-tenant setup might require whitespace-trimmed or path-based routing: ```nginx location /api/ { if ($omit_not_empty($env:REQUEST_URI) && $env:REQUEST_URI ~* ^/api/) { proxy_pass http://backend:3000; } } location /public/ { root /ui; autoindex on; deny all; } ``` Avoid overly broad `allow` directives—precision limits unauthorized access.
Sync Network and Container Readiness In Docker, network readiness is critical. Use ` Мексику healthcheck` in Docker Compose to pause upstream routing until services confirm readiness. For Windows containers, `port 80` must be exposed and mapped correctly; for Linux, iptables rules in containers can block Nginx if not aligned.
Respect container startup delays—skip `curl` checks during boot otherwise, proxy bypasses succeed prematurely. Validate SSL and Certificate Handling Mixed content errors often mask as 403s when SSL is configured. Use `ssl_certificate` and `ssl_certificate_key` in Nginx, and validate certificate paths with: ```bash openssl s_client -connect host.docker.internal:443 -showcerts ``` Ensure certificates chain correctly and reverse proxy forward reports with `ssl_policy` headers preserved if terminating SSL.
Misaligned TLS settings silently deny access while servers authenticate.
Each fix targets a specific dimension of Docker-Nginx interaction. Combining header enforcement, routing hygiene, health monitoring, and secure TLS handling steadily elevates reliability and eliminates 403 silhouettes.
Ultimately, resolving 403 errors in Docker-Nginx environments demands aggregating insight from logs, validating configurations, and mirroring production network flows.These fixes not only restore access but reinforce defensive design—ensuring reverse proxy layers operate as secure, resilient gatekeepers. With precise adjustments, containers communicate freely, and forbidden becomes obsolete. For enterprise deployments, treating 403 errors as signals—not roadblocks—fuels faster troubleshooting and robust infrastructure resilience.



Related Post

Kylayesenosky: The Rising Star Redefining Social Media Engagement in 2024

Mick Jagger’s Grandkids: Heirs of a Rock Revolution Born in Modern Fire
From Country Stardom to Unlikely Icon: The Surprising Legacy of Shania Twain’s Diaper Humor

Watch Pluto TV In Spanish: Your Easy Guide to Stream Bolivia’s Favorite Channel Anytime, Anywhere

