Fix: Invalid Key Supplied Error in Laravel Passport – Why It Happens and How to Resolve It
Fix: Invalid Key Supplied Error in Laravel Passport – Why It Happens and How to Resolve It
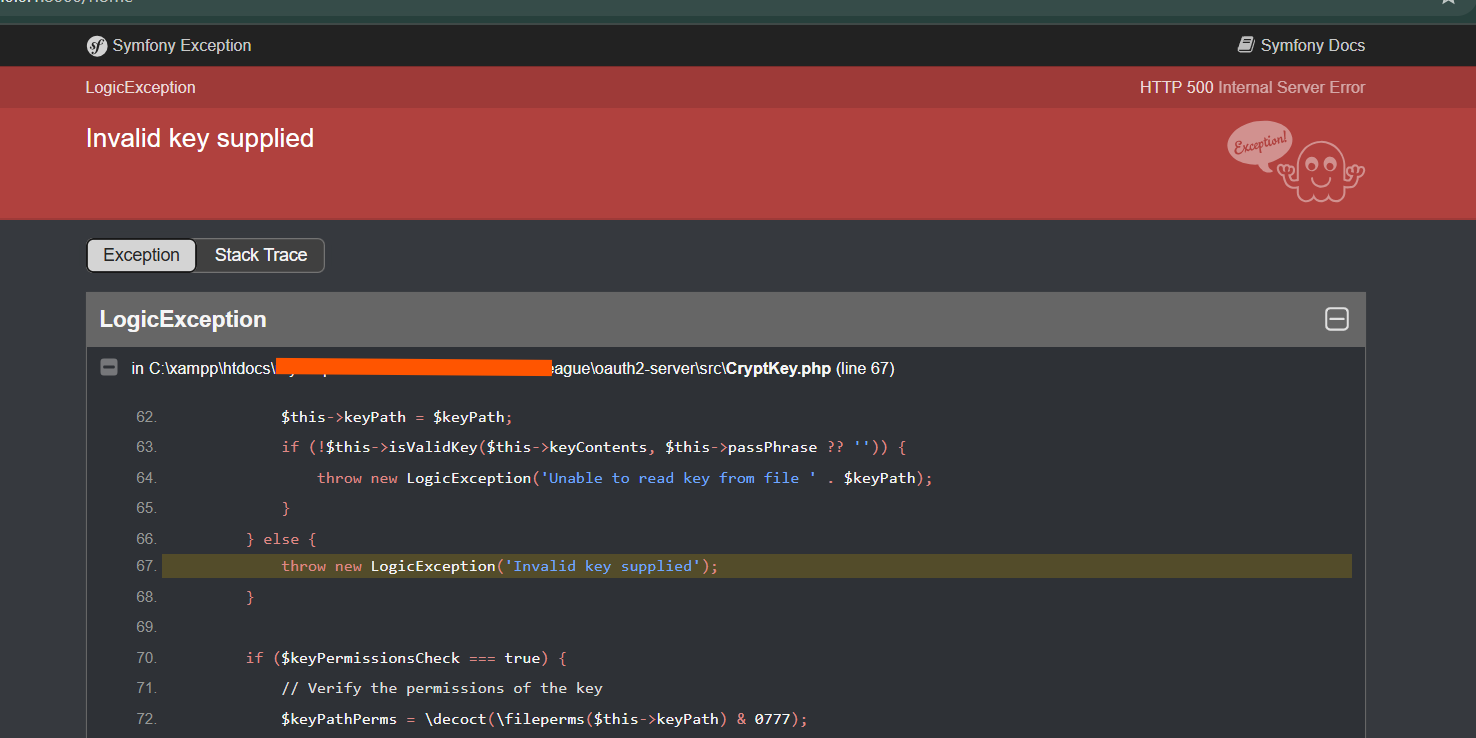
In the complex ecosystem of Laravel Passport, one persistent error lingers like a stubborn bug: the “Invalid Key Supplied” exception. Often surfaced during authentication or access token generation, this cryptic message — while brief — signals deeper misconfigurations within API key handling. For developers building secure, token-driven applications, understanding the root causes and remedies for this error is not optional—it’s essential to maintaining reliable authentication flows.
This article dissects why the “Invalid Key Supplied” error emerges, explores common triggers, and delivers actionable fixes to restore smooth operation.
At its core, the “Invalid Key Supplied” error in Laravel Passport indicates that the required authentication key—whether an OAuth access token or an API key—has been sent in an incorrect or malformed format. The Passport package validates incoming keys against expected patterns and storage locations; when a mismatch occurs, the system rejects the request with this precise error.
According to official Laravel documentation, the key must be accurately rendered, typically base64-encoded for token transmission, and include exact formatting such as `Bearer Root Causes Behind the Condition
The error rarely stems from a simple typo; instead, it often reflects systemic issues in how keys are delivered, stored, or referenced.
Several interrelated factors frequently underpin the failure: - **Incorrect Header Syntax**: One of the most common culprits is malformed request headers. Passport expects keys embedded within standard or custom headers such as `Authorization: Bearer
- **Key Mismatch in Storage**: The authentication provider—be it Redis, a database, or memory cache—may expect a specific key format. If the stored token or key differs—due to casing mismatches, trailing spaces, or encoding errors—Passport rejects it as invalid. - **Framework Version Incompatibilities**: Laravel and Passport evolve rapidly.
A key correctly formatted in one release may break when upgraded due to changes in how tokens are parsed or validated. Using outdated dependency versions without proper upgrade checks compounds this risk. - **Environment or Strategy Misconfiguration**: Passport supports multiple authentication strategies—API tokens, sessions, OAuth2, etc.
Misalignment between the configured strategy and how keys are issued or retrieved leads to missing or invalid keys by design.
Step-by-Step Resolution Guide
Resolving the Invalid Key Supplied error demands a systematic approach, targeting key accuracy, format consistency, and deployment alignment. The following steps provide a proven troubleshooting framework:- Validate Header Structure: Ensure `Authorization` or custom headers follow strict formatting.
Use `Bearer ` (note the space) consistently and confirm tokens have no trailing whitespace. Test header content using tools like Postman or curl to isolate syntax flaws.
- Confirm Token Integrity: Regenerate tokens via Laravel’s token management methods (`garbage()`, `create()`, or `createAndSend()`) to ensure clean, exact key values. Compare stored tokens with newly issued ones to eliminate discrepancies.
- Audit Authentication Middleware: Middleware like `Laravel\Passport\AuthorizeHttpMiddleware` must match the access strategy.
Verify route definitions use consistent strategy flags (`api`, `auth api`) and controller traits like `HasApiTokens`.
- Sync Environment Settings: Cross-check Passport’s `$passport` configuration—including `tokenName`, `scopes`, and `issuer`—against database entries and runtime environments. Even a single letter mismatch breaks key validation.
- Upgrade Securely: When updating Laravel or Passport, run `composer update` and review deprecation notices. Use version compatibility tables to prevent breaking changes in key serialization logic.
For developers working in high-velocity environments, implementing automated request validation and header sanitization adds resilience.
Middleware hooks that strip invalid characters before token verification can prevent errors before they surface. Additionally, logging request headers—while masking sensitive data—helps identify patterns in invalid key submissions, accelerating root cause diagnosis.
Real-World Scenarios and Betterness
Consider a mobile app attempting to fetch protected resources.The app sends an access token encoded in a Bearer header, but the server trims spaces from header values, introducing invisible Nano whitespace that breaks validation. Or a refresh token generated in one environment produces a lowercase key instead of uppercase, mismatched by Laravel’s strict comparison. These subtle flaws expose how even minor deviations from expected formats derail authentication.
However, the same debugging rigor that identifies the issue also strengthens security—ensuring only properly scoped, formatted keys pass through, blocking rogue actors who exploit formatting weaknesses.
The “Invalid Key Supplied” error in Laravel Passport is not a failure of the framework itself but a symptom of attention to detail in configuration and implementation. It underscores a fundamental truth: API security hinges on consistency between client behavior and server expectations.
By methodically validating headers, auditing token lifecycles, and aligning environment settings, developers not only resolve the error but elevate the reliability and robustness of their authentication infrastructure. In an era where access tokens are attack surfaces, precision in key handling is non-negotiable. Mastering these nuances transforms a recurring frustration into a safeguard—solidifying trust in every token issued and every request authorized.



Related Post
How Diddy Combs Intoxication Defense That Silences Critics Without Blinking

Gia Duddy Video Exposes Her Rise—Behind the Fame, Strategy, and Unseen Grit

The Electric Rebellion of Abbey Lee Kershaw: Mad Max Meets Fashion Frontiers

Unlocking Time: The Precision of Tithi Details in Mathrubhumi Malayalam Calendar 2003

