How Do I Private Call Someone: The Essential Guide to Secure, Discreet Communication
How Do I Private Call Someone: The Essential Guide to Secure, Discreet Communication
In an era defined by constant digital noise and unrelenting surveillance, the ability to make a private, undisturbed call has become both a practical necessity and a growing privacy concern. Whether to protect sensitive information, maintain discretion in personal or professional matters, or simply avoid unwanted interruptions, learning how to private call someone empowers users to reclaim control over their communication. This article reveals the step-by-step process, essential tools, hidden nuances, and legal boundaries surrounding private calling—offering actionable guidance for anyone seeking secure, confidential contact.
At its core, a private call refers to a voice conversation not accessible to third parties—phone networks, ISPs, or even the Stanford Digital Privacy Lab’s recommended measurement utilities—ensuring confidentiality. Unlike traditional calls, which traverse public infrastructure vulnerable to interception, private calling relies on encrypted channels that encode audio in real time. This technological layer shields conversations from passively listening eavesdropping or active surveillance.
The growing demand for privacy has spurred adoption of apps, devices, and protocols designed to make private calling accessible even to non-technical users.
Why Private Calls Matter in Modern Communication
Modern life operates on a paradox: while connectivity enables seamless interaction, it simultaneously exposes individuals to unprecedented risks. Every call on standard networks risks exposure through metadata, network metadata harvesting, or even direct interception. Private calling disrupts this cycle by creating a private, encrypted tunnel between caller and recipient.- **Protecting Sensitive Information:** Medical records, legal strategy discussions, financial advice, or business negotiations require discretion. Unprotected calls reveal caller-identified metadata to carriers or third-party servers, risking exposure. - **Avoiding Surveillance:** Governments, corporations, and bad actors monitor communications.
Private calls reduce digital footprints, enhancing personal and digital security. - **Preserving Privacy in Private Spaces:** Domestic settings, workrooms, or crowded public spaces often necessitate private conversations. Traditional phones fail here—many rely on unencrypted broadcast signals.
In professional contexts, private calls reduce miscommunication risks by enabling clear, secure dialogue—especially critical in high-stakes industries like healthcare or legal services, where HIPAA or GDPR compliance hinges on privacy safeguards.
Methods to Make a Private Call: Tools and Techniques
Achieving a truly private call requires choosing the right mix of technology, protocol, and best practices. Multiple approaches exist, each with varying levels of complexity and security assurance.### Encrypted Messaging with End-to-End Encryption Modern messaging platforms such as Signal, Threema, or Wire offer end-to-end encryption (E2EE) that secures voice (via secure voice codecs) and text.
While not perfect—since metadata like contact lists remain visible—E2EE ensures only intended recipients decrypt the call. For example, Signal’s hosted call feature automatically encrypts both audio and metadata, requiring no setup beyond installing the app. Users in conflict zones or repressive regimes increasingly rely on Signal, with reports showing its use surged by over 40% in 2023 amid rising digital repression.
Using Virtual Private Networks (VPNs) to Obscure Signal Paths
Even encrypted calls remain vulnerable if ISPs track call metadata.A trusted VPN masks your IP address and encrypts internet traffic, making it harder to link calls to your location or identity. When combined with secure apps, a VPN adds a critical layer: customers using a U.S.-based VPN while calling abroad reduce metadata exposure, according to the Electronic Frontier Foundation (EFF). However, VPN choice matters—open-source solutions like ProtonVPN or Mullvad are preferred over free services that may log data.
Push-to-Talk and Secure Hotline Services
Dedicated push-to-talk (PTT) services, such as Wiza or certain enterprise communication platforms, offer “private talk” features that simulate radio-style call privacy over cellular or VoIP networks. These services auto-encrypt alerts and disable call logging, ideal for journalists, activists, or teams needing silence during sensitive operations. Unlike standard apps, they prioritize discretion with features like silent party rooms and anonymous callbacks.For example, some secure PTT tools use one-time audio tokens, erased immediately after transmission.
SIP Trunking and Private Networks for Organizations
Businesses require scalable, secure private calling through SIP (Session Initiation Protocol) trunking, where encrypted voice calls route through private VoIP gateways. Systems like Cisco Webex or RingCentral integrate SIP with E2EE and ROCSP (Red Activation of Calls to Privacy Services), ensuring voice data stays within approved, monitored networks.These solutions support call recording (when consented), call analytics, and granular access control—critical for compliance with regulations like CCPA and GDPR.
For personal use, simple tools like Signal or WhatsApp suffice; professionals facing high-risk environments benefit from layered solutions combining E2EE, VPNs, and purpose-built PTT. Communities such as journalists in authoritarian states or whistleblowers now share standardized protocols, including pre-authorized secure channels with trusted contacts.
Practical Steps to Conduct a Private Call Safely
Even with advanced tools, effective private calling demands attention to user behavior.Key practices include: - **Verify Caller Identity:** Use out-of-band confirmation (e.g., calling back on a known number) to prevent phishing via fake caller IDs. - **Minimize Metadata:** Disable call logs and push notifications. Avoid sharing personal details unless conversation context demands them.
- **Check Encryption Status:** Confirm E2EE is active—signal icons, secure audio tunnels, and encrypted metadata logs serve as visual cues. - **Use Separate Devices:** Original hardware or burner phones reduce tracking risks; avoid reusing devices linked to primary accounts. - **Wireless Network Awareness:** Connect to trusted, secure Wi-Fi; public hotspots remain prime interception points.
Use mobile data only when unavoidable, if encrypted. Apps like Signal show clear indicators—green security ticks for E2EE, status messages confirming disconnection—helping users verify privacy in real time. Similarly, Dedicated secure PTT platforms label call statuses as “private” or “anonymous,” eliminating guesswork.
Legal and Ethical Considerations
Using private calling tools is legal in most jurisdictions, but intent matters. In democratic countries, privacy rights are protected under constitutional or human rights laws—except when communications involve illegal activity. Ethically, private calls should respect others’ privacy: avoid extensions without consent, especially in professional or blended personal-professional settings.Journalists, activists, and legal professionals often navigate this carefully, balancing source protection with accountability.
Balancing Privacy and Usability: The Trade-offs
While private calling enhances security, it introduces complexity. Setup barriers exist—especially for less tech-savvy users—with app installations, key verification, and key concepts like E2EE requiring education.Over-reliance on “black-box” tools can foster a false sense of omnipotent privacy; no system is fully unhackable. Users must weigh convenience against protection—text messages suffice for casual talks, but legal strategy calls demand higher security.
Emerging technologies promise to simplify this balance: AI-driven voice scrambling may soon embed seamless encryption without user input, while zero-knowledge verification eliminates manual key checks.
The rise of decentralized networks could shift private calling toward user-controlled, peer-to-peer models, reducing reliance on central servers vulnerable to infiltration.
The Future of Secure Voice Communication
As digital interception grows more sophisticated, the demand for reliable private calls continues to grow across personal, professional, and civic spheres. Innovations like quantum encryption—where keys are theoretically unbreakable—loom on the horizon. Regulatory evolution, including stricter data minimization laws, will further push developers to prioritize user privacy by design.What remains constant is this: private calling is not just a technical feature, but a cornerstone of digital autonomy in an interconnected world.
Mastering how to private call someone involves selecting the right tools, practicing disciplined habits, and understanding legal and ethical contexts. In a world where privacy is increasingly fragile,—notifying someone you’re calling privately—while verifying their security posture—turns communication into a protected act, safeguarding trust in every voice.




Related Post

How Do I Private Call Someone: Mastering Secure, In-Depth Communication

The Cast Behind Dunkirk: How Realism Was Forged on Screen

CS:GO on Steam: Separating Fact from Fiction — Is It Really Free-to-Play?
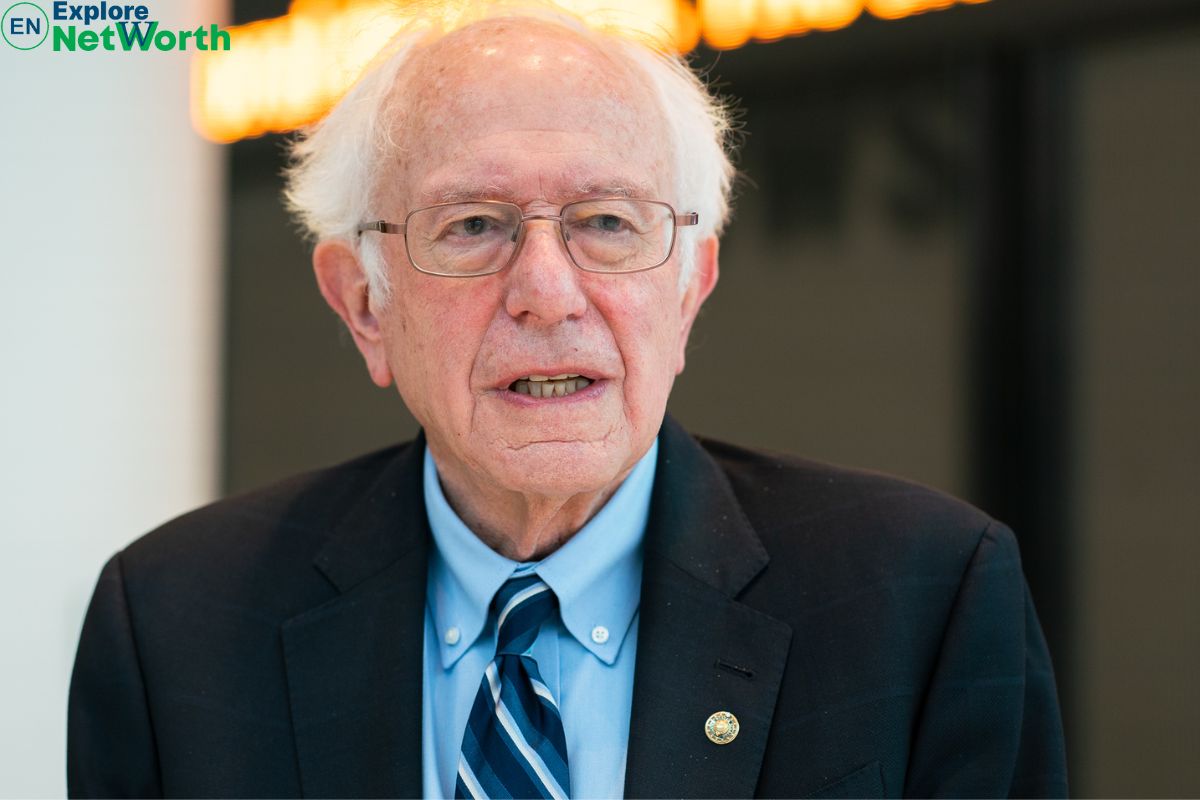
Why Bernie Sanders’ Net Worth E28093 Is Igniting Headlines: Inside the Untold Secrets Fueling His Second Campaign Push

