Mytrueidentity Scam Understanding The Risks And Protecting
In an era where digital identity is currency, the Mytrueidentity scam has emerged as a chilling reminder that even well-protected individuals are vulnerable to sophisticated identity theft schemes. These scams exploit trust, leverage personal data, and manipulate psychological triggers to deceive victims into surrendering sensitive information or money. Understanding the mechanics, red flags, and actionable protections against Mytrueidentity fraud is not just precautionary—it’s essential for preserving personal and financial security in a hyper-connected world.
The Mytrueidentity scam relies on impersonation and data exploitation, frequently using stolen or fabricated personal identifiers—names, Social Security numbers, healthcare records, or biometric details—to feign legitimate relationships or service providers.
Victims may receive phishing emails, fake customer service calls, deathly urgent messages, or social media impersonations claiming urgent help is needed. “These scammers mimic trusted entities—banks, government agencies, or even family members—to bypass skepticism,” explains cybersecurity analyst Dr. Anna Reyes.
“They create a false sense of legitimacy through polished messages, fake IDs, and urgent demands.” Transactions often begin with small requests—password resets, verification codes, or wires—escalating into irreparable financial loss or identity compromise.
Unmasking the Tactics: How Mytrueidentity Scammers Operate
Mytrueidentity schemes follow predictable patterns designed to exploit human behavior and digital trust.
- Phishing & Spear Phishing: Attackers send hyper-personalized messages using harvested data, making them far more credible than generic scams. A message referencing a recent purchase or medical appointment increases credibility by a significant margin.
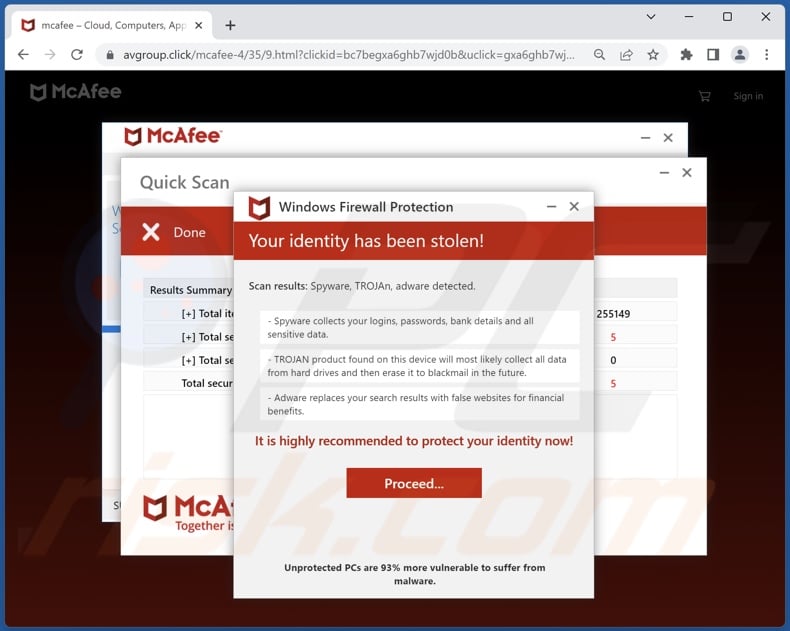
- Impersonation via Voice & Mail: Scammers use voice-cloning technology or fake websites mimicking official services to trick victims into sharing credentials or wiring funds.
- Social Engineering Loops: Once initial contact is made, scammers build rapport slowly—gaining trust before demanding access to sensitive data or funds.
- Emergency Exploitation: Urgency is a key weapon: fake alerts about suspended accounts, unpaid fines, or family emergencies create psychological pressure, reducing victims’ rational decision-making.
Real-world examples reveal the stealth and impact of Mytrueidentity scams.
In 2023, a coordinated campaign targeted Medicare beneficiaries, using fake insurance messages to steal personal and financial data, resulting in over $2 million in fraudulent transfers. Meanwhile, educators and students have fallen for fake scholarship websites masquerading as legitimate funding sources, harvesting login details and banking information. Even corporate employees have been duped via “urgent” internal alerts mimicking IT departments, leading to corporate wire scams.
“The scammers don’t need complex tools,” warned fraud prevention specialist James Tran. “They use psychological manipulation paired with stolen data to infiltrate systems disguised as trusted entities.”
Identifying a Mytrueidentity scam begins with vigilance. Common warning signs include:
- Irregular contact methods—unexpected calls, texts, or communications via unofficial apps or unknown phone numbers.
- Requests for sensitive information via email, text, or unsolicited phone—legitimate organizations rarely ask for passwords, SSNs, or banking details out of the blue.
- Poor grammar, odd formatting, or mismatched URLs in messages, though skilled scammers often bypass this.
- Urgency or threats of account lockout, fines, or legal consequences.
- Inconsistencies in caller ID, caller name, or official branding details.
Protecting oneself from Mytrueidentity scams demands a layered strategy combining technology, awareness, and behavioral discipline:
Technical Safeguards: Enable two-factor authentication (2FA) on all accounts, use password managers, avoid reused passwords, and install reputable antivirus and anti-malware software. Enable email filters to flag suspicious messages and configure browsers and email clients to block known phishing domains.
Behavioral Habits: Never share personal or financial data in unsolicited communications. Verify all requests through official channels—call the company directly using verified contact info, not links in the message. Never wire money or provide login credentials in response to unexpected demands.
Education & Awareness: Regularly review scam trends through official cybersecurity reports (e.g., FTC, IC3, or industry threat intelligence). Stay updated on new techniques targeting Mytrueidentity data—such as AI-generated voice scams or deepfake impersonations.
Anti-scam organizations like the Federal Trade Commission emphasize that “awareness is your first line of defense.” Training personal and professional networks to spot anomalies reduces the scammer’s success rate dramatically.
Perhaps most critical is cultivating a mindset of skepticism without paranoia.
No legitimate institution will demand immediate action via untraceable channels or threaten dire consequences over text or email. When in doubt, pause. Verify.
Respond only through trusted, independently confirmed methods. This cautious approach transforms passive users into active protectors of their identity.
In an age where digital presence defines much of personal identity, the Mytrueidentity scam underscores a sobering truth: vulnerability is not just a technical flaw, but a behavioral one. While technology evolves to counter fraud, human judgment remains the ultimate filter.
By understanding scam mechanics, recognizing red flags, and implementing proactive protections, individuals can reclaim control over their digital identity—turning awareness into empowerment and reducing risk in an increasingly deceptive online landscape.
Summary of Key Protective Moves
- Verify all urgent requests through official, independently accessible channels.
- Enable multi-layered authentication and strong, unique passwords.
- Educate yourself on evolving scam trends and spoofing tactics.
- Adopt a “verify before acting” mindset across digital communications.
These actions, consistently applied, form a resilient barrier against Mytrueidentity threats and reinforce long-term identity safety in a world where trust is both a necessity and a vulnerability.


Related Post

Markie Posts Husband And Kids All We: Life, Love, And Legacy in a Modern Family Tale

Brigette Macron: Architect of French Political Resilience in a Turbulent Era

Free Fire ID: Is Using a Fake ID Legal? What You Need to Know

Joe Massino: Architect of Teamsters’ Strategy in the Modern Arena

