Unlock ENM: How Enigma Machine Decryption Shaped Modern Cybersecurity
Unlock ENM: How Enigma Machine Decryption Shaped Modern Cybersecurity
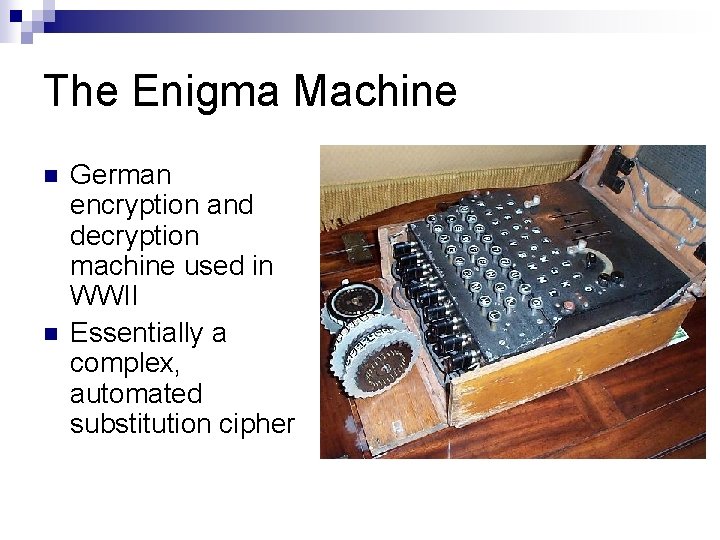
In an era defined by digital vulnerability, the legacy of ENM—central to the Enigma machine’s operation—reveals foundational principles still driving cybersecurity innovation. Originally developed to obscure military communications, the Enigma machine’s mechanical complexity and cryptographic rigor laid the groundwork for modern encryption, proving that secure communication hinges on asymmetry, unpredictability, and controlled access. Today, the concept of ENM transcends its historical roots, serving as a blueprint for protecting data in an interconnected world.
The Cryptographic Engine Behind ENM
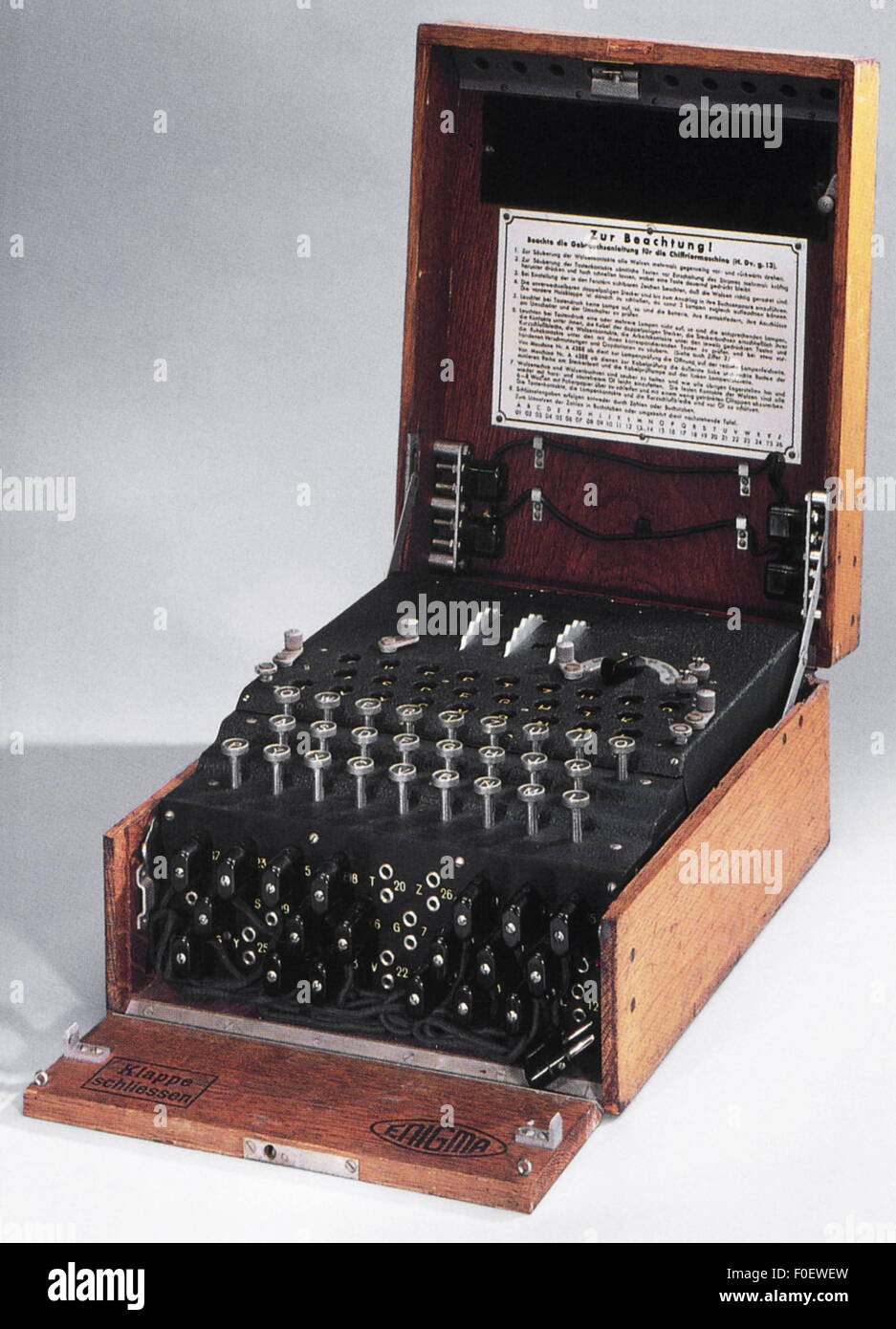
At the heart of ENM’s power was its electro-mechanical encryption system, utilizing rotors, plugboards, and reflectors to transform plaintext into unrecognizable ciphertext.
Each key press shifted internal components through a series of precise mechanical pathways, generating an ever-changing substitution cipher that defied classical breaking methods. The rotors—typically three or more—rotated with every letter, continuously altering the encryption path and ensuring that identical plaintexts produced unique ciphertexts. This ratchet mechanism, combined with the plugboard’s ability to swap character pairs, produced an exponential increase in possible codes—making brute-force attacks impractical at the time.
As noted by historian of cryptography David Kahn, “The Enigma machine didn’t just encrypt messages; it engineered complexity.”
Plugboard permutations expanded cryptographic depth by manually jumpping five pairs of letters before and after rotor transitions. With 10 standard beads and 10 adjustable jumper wires, the number of plug connections blossomed to over 150 million combinations. When multiplied by rotor configurations and ring settings—adjustable positions that shifted internal letter mappings—the Enigma system created an astronomical key space.
“Each layer of encryption introduced deliberate entropy,” explains security expert Dr. Elena Vasquez, “making cryptanalysis a multidimensional challenge long before computers existed.”
Human Factors: The Weak Link in ENM’s Security
While the Enigma’s mechanics were sophisticated, human error often eroded its defensive strength. Operators, trained to maintain efficiency, sometimes repeated commands or leaked procedural details.
Worse, methodical missteps—such as predictable key changes or failure to warrant cables—provided cryptanalysts critical footholds. Polish mathematicians like Marian Rejewski exploited such patterns, identifying weaknesses not in the machine itself, but in its operational protocols.
Key management flaws amplified vulnerabilities. Frequent rotor rotation schedules were inconsistently applied, and unused rotor racks were often shared or documented, enabling adversaries to build comprehensive frequency analyses.
Historical records confirm that intelligence agencies meticulously monitored traffic and exploited procedural blind spots. “The machine was flawless in design but brittle in execution,” notes cryptanalysis historian Henry Roberts, “the true enemy wasn’t the rotor but the person operating it.”
ENM’s Enduring Legacy in Modern Encryption
Though ENM vanished from battlefield use after World War II, its cryptographic DNA persists in contemporary systems. The emphasis on layered defenses—combining multiple algorithmic barriers—mirrors modern encryption’s defense-in-depth architecture.
Ransomware-resistant protocols, multi-factor authentication, and secure key exchange mechanisms all trace intellectual lineage to Enigma’s principles of obscured transformation and access control.
Public-key cryptography, which enables secure digital communications without shared secrets, evolves the Enigma’s core insight: unpredictability is cobbled from complexity. Asymmetric encryption platforms like RSA and ECC depend on mathematical Chasm—equally difficult to reverse as the Enigma’s cipher paths—but grounded in digital verifiability. ENM’s switch-based architecture inspired engineers to design systems where decryption requires private keys, not brute force.
“The Enigma proved that secrecy needs both transformation and trust,” observes cybersecurity researcher Sarah Kim, “and today’s standards uphold that balance.”
The Enigma machine’s history serves not as a relic, but as a cautionary yet instructive model. Its mechanical vulnerabilities reveal that no system remains secure without human discipline and adaptive defense. In the ongoing battle for data integrity, the lessons embedded in ENM’s design continue to shape how we encrypt, authenticate, and protect information—ensuring that the spirit of secure transformation lives on in every encrypted message sent across the globe.
Underlying every secure connection, from bank transactions to secure messaging, is a quiet inheritance from ENM.
Its intricate web of rotors and switches taught the world that true security emerges not just from technology, but from understanding the interplay between code, human behavior, and relentless innovation.

Related Post

Patricia Nonnenmacher and the Twin Identity: Unraveling the Mystery of Gi

Patricia Nonnenmacher’s Twin Legacy: Unraveling the Identity of Gi in a Unique Sibling Dynamic
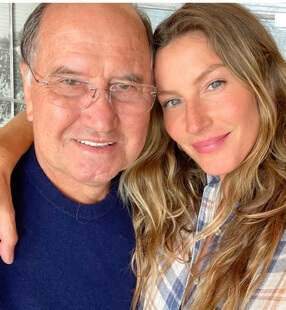
The Enduring Influence of Patricia Nonnenmacher Bündchen: Trailblazing Style, Sport, and Purpose

Rafaela Nonnenmacher Bündchen: The Rising Guardian of Healthy Living in Chile’s wellness Frontier