Unlocking Connections: How Your Phone Number Reveals People Across the USA
Unlocking Connections: How Your Phone Number Reveals People Across the USA
In an era where digital footprints define modern life, locating individuals using just a phone number has become both a powerful tool and a sensitive issue. The ability to trace a person’s location or identity through telecommunication data hinges on precision, legal boundaries, and evolving privacy norms. While telecom systems and data brokers wield sophisticated networks capable of linking numbers to real-world identities, the rise of precision location finding raises urgent questions about consent, ethics, and the boundaries of digital surveillance in the United States.
This article explores how phone numbers still serve as gateways to pinpointing people—how the interplay of technology, data infrastructure, and regulation shapes the modern pursuit of connection and contact.
The foundation of finding individuals via phone number in the U.S. lies within a complex ecosystem of telecom providers, data aggregators, and location-tracking mechanisms.
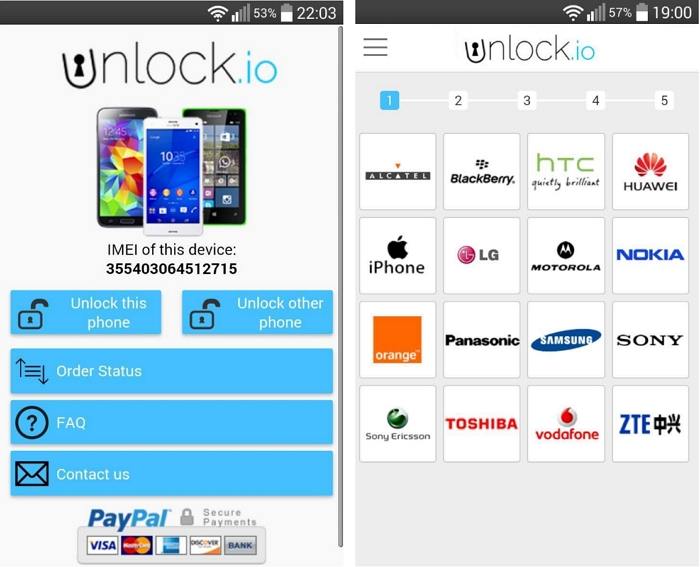
Unlike landlines of the past, today’s mobile numbers are dynamically tied to cellular towers through cell-site signaling and IMEI (International Mobile Equipment Identity) data. When a phone connects to a network, it broadcasts a unique identifier linked to a specific location—an anchor point in spotting a user’s general area. According to Dr.
Elena Torres, a telecommunications policy expert at MIT Media Lab, “Modern networks use triangulation across hundreds of cell towers to estimate a device’s position within meters, especially when GPS is unavailable. This precise signal matching allows service providers and authorized entities to locate users within targeted zones, often accurate to within a city block.”
But how does a simple phone number unlock such granularity? The process involves multiple layers: - **Network Registration Data**: When a number is provisioned, carriers register it with the FCC and store initial location metadata.
- **Cell-Site Records**: Mobile network operators log when a device connects to each tower, creating a historical and real-time map of user movement. - **Location Aggregators**: Firms like PhoneCheck, Spokeo, and Realsignal compile public and data-driven profiles, cross-referencing numbers with databases that include addresses, employment, and social media links. - **Vector Search Technology**: Advanced algorithms compare numeric and geospatial data patterns to identify matches or probable locations, enabling low-confidence to high-confidence identification depending on signal strength and network context.
Despite these tools’ technical sophistication, precision comes with profound privacy implications. The FCC and Federal Trade Commission enforce strict rules—such as the Telephone Consumer Protection Act (TCPA) and state privacy laws like CCPA—mandating consent before location tracking or data sharing. “Indiscriminate use of phone number data risks violating constitutional privacy rights,” warns privacy advocate Marcus Lin.
“Even if a number belongs to a carrier-selected pool, using it without opt-in authorization crosses ethical and legal lines, especially when tied to geolocation.” Location-based services promise convenience—finding lost phones or reconnecting with old friends—but often at the cost of transparent user control.
Real-world applications underscore both the promise and peril. Utility companies use number-digitized geospatial data to dispatch technicians efficiently; emergency services leverage anonymized location insights during crises; and private investigators employ licensed tech to locate missing persons or verify identities in legal matters.
Yet, high-profile cases—such as the 2022 data leak exposing over 100 million numbers with approximate locations—have demonstrated how aggregated data can create privacy black holes. “When numbers are cross-referenced with external datasets—like property records or social profiles—the risk of re-identification skyrockets,” explains cybersecurity researcher Julia Park. “One phone number can become a gateway to entire family networks or sensitive personal movements.”
To navigate this landscape responsibly, users must understand both the capabilities and limitations of phone number tracking.
While carriers keep emergency location data precise and securely stored under cell-site location information (CSLI) protocols, third-party tools often operate in regulatory gray areas. Using official services with clear disclosures, such as carrier-provided location services or vetted people-finder platforms, offers the best balance between reliability and privacy protection. Moreover, consent remains paramount: “Transparency benefits everyone,” says Lin.
“Users deserve to know when, how, and why their number’s location might be accessed—especially in research or commercial contexts.”
The technological prowess behind identifying individuals via phone number reflects telecommunications’ evolution from voice networks to data-driven ecological systems. Cell towers, algorithms, and user consent frameworks together form a fragile equilibrium—technically precise but ethically fragile. As precision location methods grow faster and more widespread, the power to find people with a single number demands not just technical skill, but a commitment to privacy, accountability, and legal integrity.
In the dense network of modern life, a phone number is more than a contact—it is a digital fingerprint anchoring identity, movement, and trust across the United States.
Understanding this interplay empowers users, policymakers, and providers alike to harness the benefits of telecommunication data responsibly—ensuring that the pursuit of connection never undermines the fundamental right to privacy.


Related Post
The Rise of the Unfiltered Digital Town Square and What It Means for Privacy

The Unveiling of a Cultural Flashpoint: Billie Eilish’s Nudes Unfold and the Frontal Gaze in the Age of Digital Obsession

Cybersecurity Breaches Hit Corporate Backbones: How Empresarial Leaders Are Redefining Privacy in the Digital Age

The Shocking Descent: Nikki Catsouras’ Death Video and the Tragic Collision of Grief, Privacy, and Public Spectacle