<strong>Verify Your Gmail Maps API Key: A Precise Step-by-Step Guide to Secure and Validate Access</strong>
Verify Your Gmail Maps API Key: A Precise Step-by-Step Guide to Secure and Validate Access
Navigating the world of location-based APIs can be challenging, especially when securing access to sensitive services like the powerful mapping capabilities of the General Distribution and Plataforma de Mapas do GPS (commonly accessed via the G-Maps API). For developers and businesses integrating this tool into applications—be it ride-sharing platforms, delivery services, or location-aware tools—verifying your API key application is not just a formality, but a critical step in maintaining security, preventing unauthorized use, and ensuring smooth operation. This detailed, expert walkthrough explains the essential steps to verify your G-Maps API key efficiently and reliably, transforming a potential vulnerability into a confidence-boosting milestone.
At the core of secure API integration lies validation—confirming that the key you hold belongs to an authorized user or registered project, and is correctly configured for intended use. Backing your system with a verified G-Maps API key ensures data integrity, compliance with usage policies, and real-time access to map data, routing tools, and geospatial analytics. Without this verification, applications risk blocked requests, service disruptions, and exposure to fraudulent activity.
Understanding the Role and Risks of a G-Maps API Key
The G-Maps API key acts as a digital gatekeeper, unlocking a suite of location intelligence tools provided by Alphabet’s mapping infrastructure.Whether embedding interactive maps, calculating routes, retrieving transit data, or enabling location targeting, every API call reliant on this key demands rigorous validation. A misconfigured or unvalidated key can lead to unexpected costs, data breaches, or complete service suspension. According to public documentation and community best practices, developers must treat API key validation not as an optional step but as a fundamental pillar of responsible API deployment.
Step 1: Access the Official G-Maps API Console
Begin by visiting the official G-Maps API portal—this centralized dashboard is designed specifically for managing, generating, and verifying API credentials. From there, navigate to the [API keys section], typically found under developer or account settings. If access is restricted, you may be prompted to authenticate using your project credentials or re-enter verification details previously confirmed during key creation.“Securing access starts with directing traffic to the right endpoint,” says one industry expert. “Verify your key at the source—before integrating deeply into your application stack.”
Step 2: Confirm Key Activation and Status
Once logged into the console, locate your active G-Maps API key. Each key displays clear status indicators—active, deactivated, suspended, or pending.Verify that “Active” status is confirmed and that any limitations—such as API call quotas, region restrictions, or device permissions—match your deployment needs. A key flagged as suspended or expired should immediately trigger re-activation, as ongoing service depends on live credentials. Monitor activation timestamps and verify synchronization across devices or authentication layers to avoid sudden access drops.
Step 3: Validate with Development and Test Environments
Before rolling out to production, test your API key in controlled sandbox or staging environments. Use public mapping endpoints (such as reverse geocoding or traffic data APIs) to execute sample requests and confirm correct responses. A valid key should return accurate, complete geospatial data without errors.“Always verify functionality with real-world API calls in test spans,” advises prominent developers, “before assuming reliability in live use.” This step helps catch misconfigurations—like outdated SDKs, incorrect endpoint URLs, or misaligned authentication tokens—early in the development lifecycle.
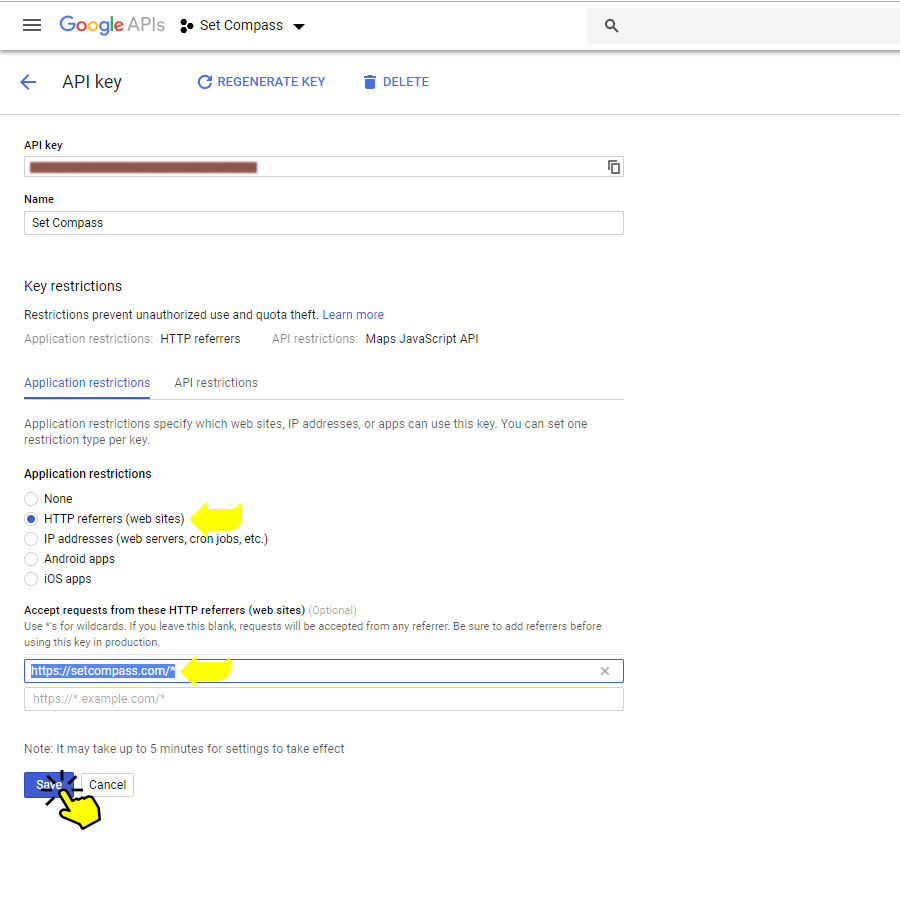
Step 4: Cross-Check Security Settings and Permissions
Verification isn’t limited to activation status; it includes validating security configurations. Review associated project settings to confirm API key scopes are properly limited—restricting access only to necessary endpoints (e.g., core maps, directions, predictions) prevents over-exposure.Enable logging and usage alerts within the API console to monitor suspicious activity in real time. “Security through precision,” notes a cybersecurity specialist, “means limiting permissions and continuously auditing key usage patterns to detect anomalies.”
Step 5: Use API Testing Tools to Automate Validation
Leverage open-source and commercial API testing platforms—such as Postman, Insomnia, or custom scripts—to automate key verification. These tools streamline repetitive validation by sending structured requests, parsing JSON responses, and flagging errors instantly.Scripted automation ensures consistency across environments and reduces manual effort, especially during key updates or system upgrades. Embedding these validations into CI/CD pipelines further strengthens reliability, ensuring every deployment checks the key’s validity before going live.
Final Best Practices for API Key Verification
Maintaining a verified G-Maps API key goes beyond a one-time check.It requires proactive management: regularly review key status, rotate credentials when needed, stay updated on API changes, and use monitoring dashboards to maintain transparency. According to API security frameworks, proactive validation minimizes downtime, cuts potential incident response time, and safeguards business reputation in an increasingly location-dependent digital economy. By diligently following the steps outlined—accessing the console, confirming activation, validating in test, reviewing permissions, and automating checks—developers empower their applications with both precision and protection.
In the fast-evolving landscape of geospatial technology, verification of your G-Maps API key is not a burden but a strategic imperative. It ensures secure, scalable, and trustworthy access to mapping intelligence, empowering users and businesses to navigate, analyze, and deliver location-based services with confidence.">
- Start by accessing the official G-Maps API console; secure the console as your central verification hub.
- Confirm the key’s active status and respect applied limitations through detailed console diagnostics.
- Validate functionality in staging environments using real API calls to detect early errors.
- Examine and tighten security settings—limiting API scope and enabling real-time monitoring.
- Automate key verification with testing tools and CI/CD integration for continuous assurance.
- Adopt a proactive maintenance routine to prevent future disruptions and security risks.
Ultimately, verifying your G-Maps API key is the cornerstone of responsible, resilient integration into today’s interactive mapping ecosystem. By embedding these steps into your development workflow, you transform a technical checkpoint into an essential safeguard—one that upholds performance, security, and trust in every pixel on screen.


Related Post

Lucy Worsley’s Marriage and Life: A Journey of Resilience, Reflection, and Quiet Strength
Julie Michael: The Rising Singer-Spotlight Star Who’s Ready to Redefine Hollywood’s Next Icon

Big White Ass: Unraveling the Myth, Memory, and Cultural Imprint of a Controversial Legacy

Decoding Neck Size: Beyond Vanity, Science and Culture Collide at Fox News

