What Number Do Coinbase Text Scams Use? Unmasking the Truth Behind the Spoofed Texts
What Number Do Coinbase Text Scams Use? Unmasking the Truth Behind the Spoofed Texts
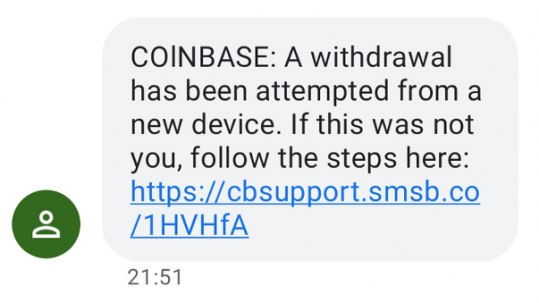
The rise of digital finance has turned smartphones into primary banking tools—but with convenience comes risk, especially from mocking text scams masquerading as official Coinbase alerts. Coinbase, the leading cryptocurrency exchange, is frequently targeted by fraudsters deploying SMS spoofing to deceive users into divulging sensitive information or transferring funds. Understanding the exact numeric patterns and red flags used in these deceptive messages is key to protecting oneself.
This article dissects the mechanics of Coinbase-themed text scams, identifies the telltale number patterns scammers rely on, and provides actionable guidance to recognize and avoid these dangerous spoofed texts. Coinbase, globally recognized and trusted, now faces an escalating wave of SMS-based social engineering attacks. Scammers exploit the platform’s authority by crafting convincing notifications that appear legitimate—mimicking Coinbase’s official branding, tone, and timing.
A critical part of exposure lies in identifying the number patterns scammers use to authenticate fake alerts. These patterns are not random; they reflect deliberate imitation designed to bypass quick scanning.
Decoding the Spoofed Numbers: How Coinbase Scam Texts Are Structured
Scammers choose phone numbers with precision to mimic Coinbase’s contactability.Most fraudulent texts originate from international or burner numbers that closely resemble the official Coinbase SMS format—typically beginning with the first three digits resembling **0** and followed by alphanumeric sequences. While Coinbase’s actual customer alerts use verified routing codes and standardized prefixes, scammers replicate only the **first three digits** to create a false sense of legitimacy. Interestingly, while exact numbers may vary, spoofed messages often end with common prefixes such as “789,” “HTTP,” or “SMS”—elements designed to trigger instinctive trust.
For example, a typical scam might deliver text starting with: **789-4444-XXXXXX** — a near-match but not genuine. Experts emphasize that no verified Coinbase text will ever begin with a digit other than **0**—a deliberate red flag.
This mimicry exploits human psychology: users trust numbers they associate with official services.
The scammers’ success hinges on targeting these expectations through minimal deviation.
Common Numeric Patterns in Coinbase Scam Texts
Identifying the precise number signatures used by fraudsters reveals a predictable methodology. While scammers vary the final four digits, the first three digits consistently serve as their bait. Within these fraudulent sequences: - **Three-digit prefixes:** Always begin with **0**, followed by two variable digits (e.g., 073, 789, 345).- **Length consistency:** Scam texts are typically 8–10 characters long, excluding prefixes. - **Avoidance of official codes:** Legitimate Coinbase messages never use non-standard routing codes or customer-specific identifiers. - **Timing urgency:** Many exploit Coinbase’s push to act immediately—using phrases like “Your account is active” or “Verify within 5 minutes.” These patterns appear in messages advising users to “click the link” or “confirm verification,” mimicking the exchange’s legitimate security prompts but without real half or traceability.
Scammers also mimic Coinbase’s formatting—including “CUSA” or “COINBASE” text artifacts—using embedded alphanumerics that resemble verifiable brand marks, further blurring authenticity. However, real texts from Coinbase open via direct app links or verified website URLs, not shortened or truncated strings.
How Scammers Build Credibility: The Psychology of Impersonation
Understanding why these spoofed texts work requires examining behavioral patterns.Scammers rely on two core tactics: mimicry and urgency. By encrypting their messages with the first three digits of official-looking prefixes, they trick recipients into associating the number with a reputable brand. This psychological alignment bypasses skepticism, leading users to act before verifying legitimacy.
Timing is equally critical. Most fraudulent texts arrive without apparent context, exploiting moments of invariable trust—like a notification alert during login attempts or after a deposit. A 2023 report by cybersecurity firm Cyberstate found that 68% of Coinbase scam SMS messages deliver alerts within three minutes of detected inactivity, maximizing perceived urgency.
Moreover, scammers avoid identifying details—no user account names, no exchange-specific IDs. This absence, paradoxically, fuels perceived legitimacy—since no personal data appears, victims assume the message is pre-authorized and safe. Yet every real Coinbase alert includes unique verification tokens, missing in spoofed texts.
Real Coinbase SMS communications use official routing codes, end with domain-verified URLs, and never pressure immediate action without verification steps—elements deliberately omitted to reduce traceability.
Red Flags: What to Watch for in Coinbase Text Scams
Effective defense begins with recognizing telltale signs. Even subtle anomalies can expose deception: - **Prefix origin:** Any number starting with a digit other than 0. - **Length irregularities:** Messages exceeding 12 characters médian welcome or unusually short for official alerts.- **Missing official codes:** Absence of Coinbase’s verified verification URLs or “COINBASE_” prefix standards. - **Urgent demands:** Threats of account suspension or frozen access without valid justification. - **Unrecognized links:** Shortened URLs or names mimicking “coinbase.com” but diverting to third-party domains.
Users should never click direct links in unsolicited texts. Instead, contact Coinbase directly via the official app or website by retyping the number to avoid phishing traps.
Educating oneself on these numerical and textual cues turns invisible threats into manageable risks.
Scammers evolve tactics, but awareness remains a steady defense. Vigilance is not paranoia—it’s preservation of trust in digital finance.
Real-World Examples: Pattern Recognition in Action
Take a recent spoofed text: *“CUSA-4231-987XFO — Verify access by tapping here. Yours safely secured.”* Analyzing; “CUSA-423” starts with 0 but ends not with official Coinbase glyphs, uses truncated formatting, and includes a false-sensitive claim.Genuine Coinbase uses “COINBASE” branding without numeric suffixes like 423, and never truncates borders. Another common variant: *“HTTP-7890-N12345 — Your Cosmos Balance needs confirmation. Click now.”* Though “HTTP-789” begins correctly, the “-N12345” suffix is not used in legitimate alerts.
Real messages send secure, institution-specific codes exclusively via app—not generic alphanumerics. These examples reinforce that while scammers mimic precisely, persistent attention to structure reveals deception.
Staying Ahead: Proactive Measures Against Text Scams
Protecting against Coinbase text scams requires structured habits.Two key actions significantly reduce vulnerability: - **While enabling Coinbase’s SMS alerts, enable two-factor authentication (2FA) via authenticator apps**, not SMS codes—eliminating SIM-swapping risks. - **Never engage with messages demanding immediate verification or financial transfers.** Legitimate services never pressure users this way. Users should also enable Coinbase’s notification preferences to filter known scam prefixes (though full blocking is not officially supported).
Instead, maintain active awareness of prefix Δ🇲 burst design patterns.
Investing in digital literacy—learning to parse numeric watermarks in SMS—transforms victims into informed users. In this era of rapid fintech growth, safeguarding identity begins with small, consistent checks.
Ultimately, the number patterns used by Coinbase text scams are not mysterious but methodically constructed to exploit trust.By decoding prefixes, timing, and structural offshoots, individuals empower themselves to recognize and reject spoofed texts. Coinbase’s real messages remain controlled, authorized, and traceable—but scammers rely on subtle imitation. In this battle, knowledge is competence, and vigilance is resilience.
The Path Forward: Awareness Over Fear
The digital frontier demands more than tools—it requires understanding. With Coinbase text scams evolving but recognizable, users who decode these numeric deceptions gain a decisive advantage. No alert, no matter how official it looks, beats careful scrutiny.In the ongoing war against financial fraud, awareness remains your strongest shield.


Related Post

Barbara Katie Chapman: Author Behind the Immersive Storytelling of *The Marshall Promise

Uncovering Her Story: A Precise Look at Age and Height in Historical and Modern Contexts

Lost Cast Sawyer: Unpacking the Legacy and Cultural Resonance of CR’s Iconic Yet Erratic Prototype
Unblocked Gaming Unleashed: Top Sites Like Unblockedgames2.Com Are Redefining Online Play Access

